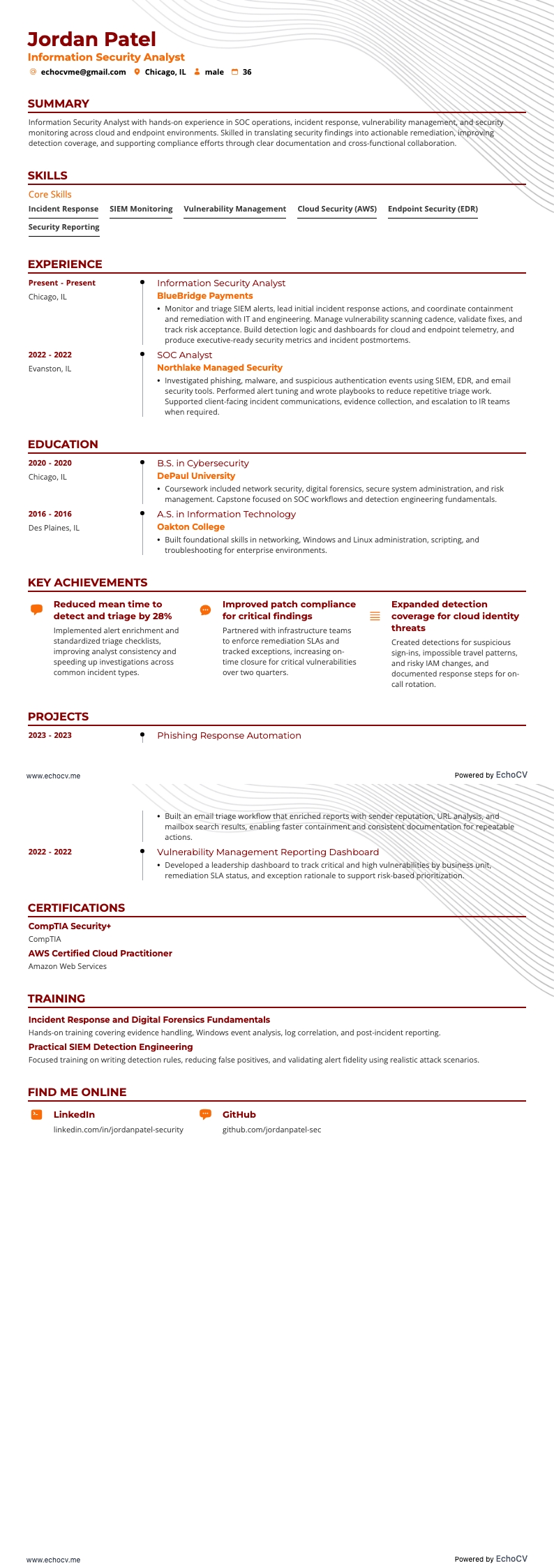
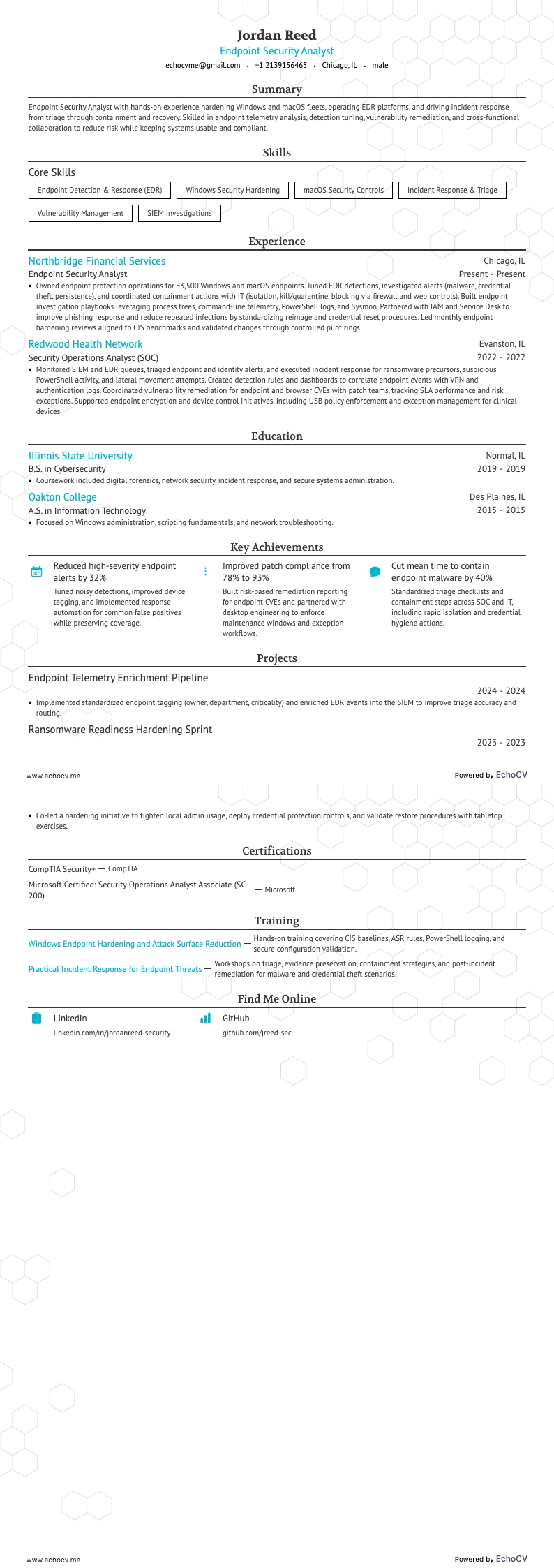
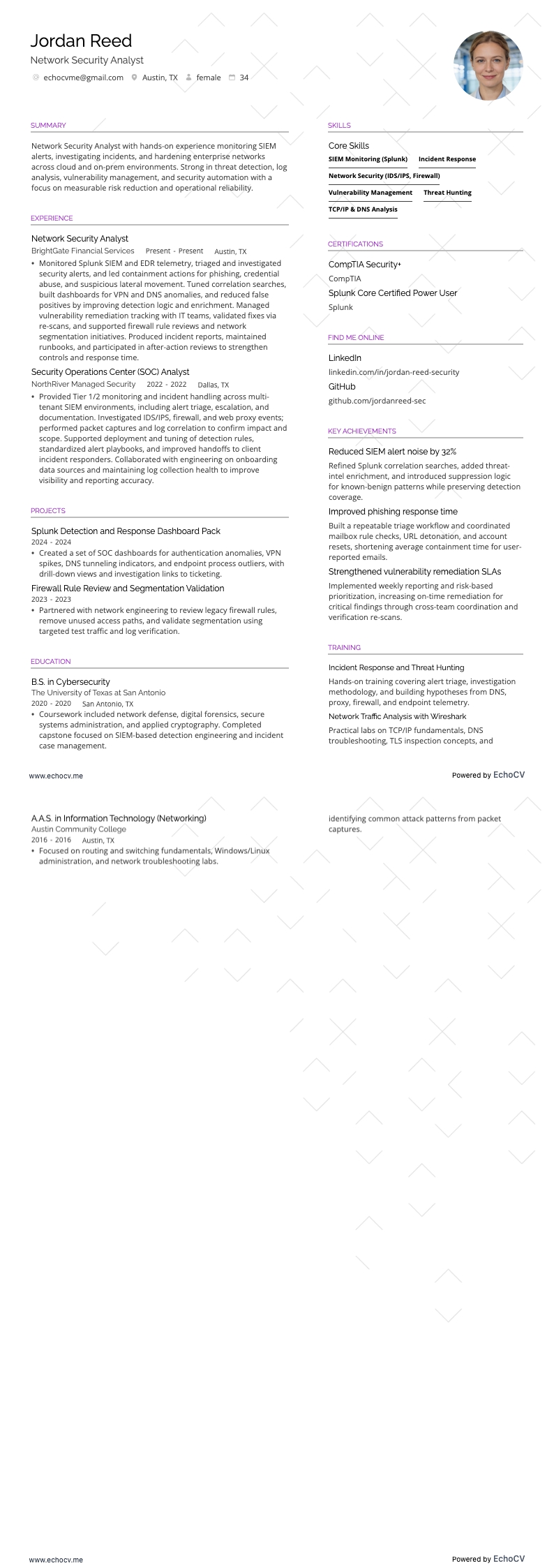
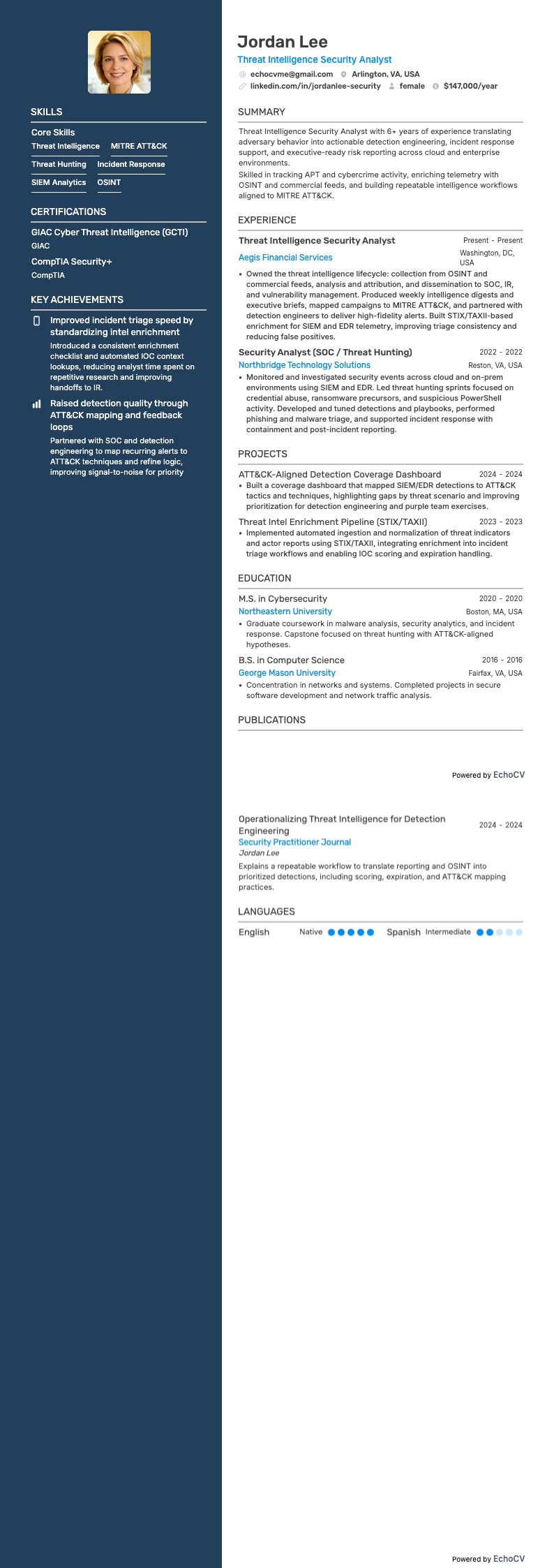
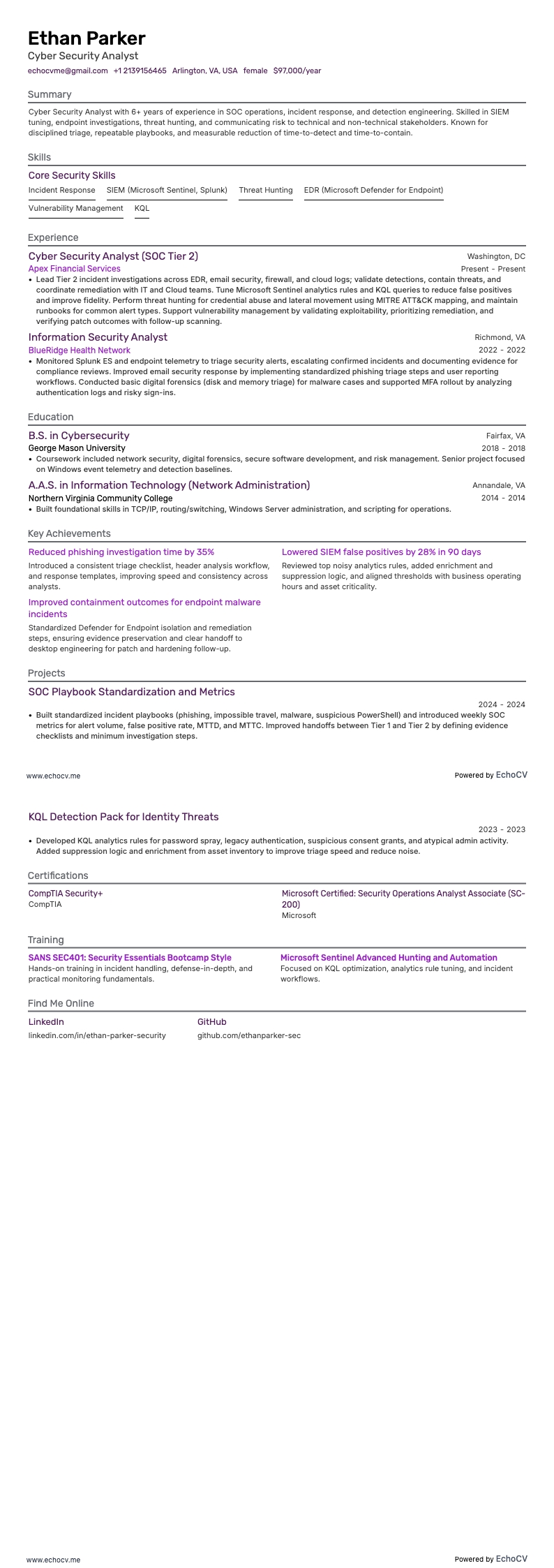
As a security analyst, you’re the frontline that turns alerts into action and threats into lessons learned. Technical chops (SIEM, EDR, SOAR, log hunting, scripting) get you noticed, but what wins interviews is clear evidence of impact: faster containment, fewer false positives, and measurable reductions in business risk.
According to the U.S. Bureau of Labor Statistics, as of November 2025, employment for information security analysts is projected to grow 29% from 2024 to 2034. Such a growth rate is much faster than average. It means security IT roles will be in demand but it will be harder to land a high-profile position.
To stay competitive, your resume should show both forensic depth and strategic thinking: how you improved detection coverage, tightened controls, shortened MTTD/MTTR, or made audits painless. In this guide, we’ll show you how to build a Security Analyst resume that leads with outcomes.